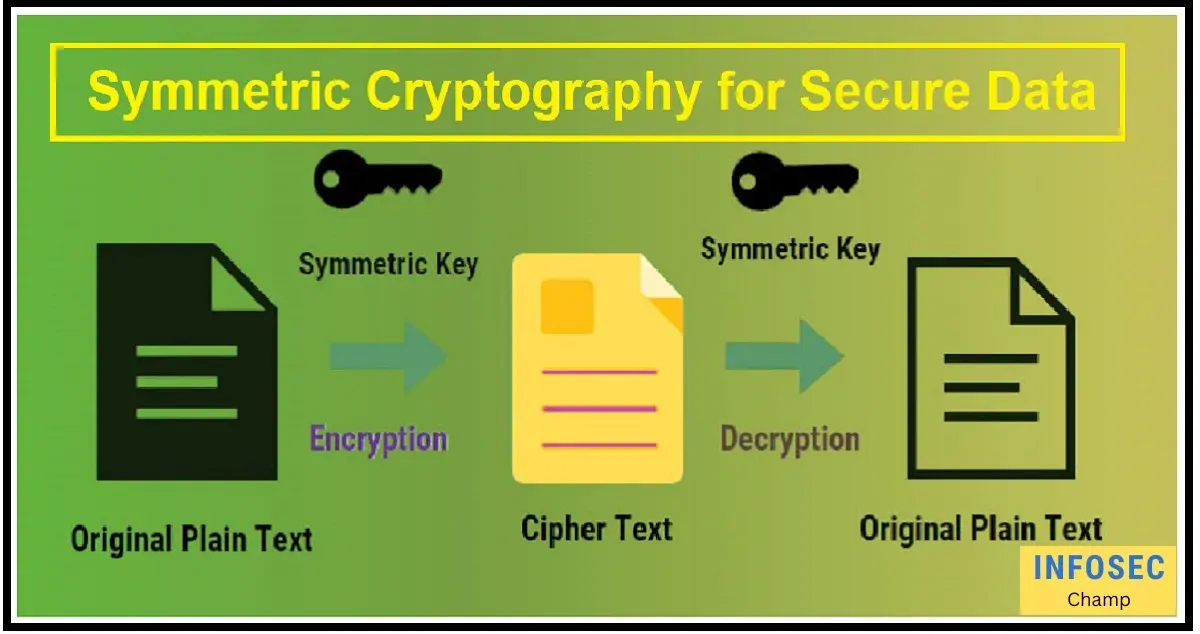
Which is not a disadvantage of symmetric cryptography; Symmetric cryptography is a widely used encryption technique that employs the same secret key for both data encryption and decryption. While this encryption method undoubtedly has certain problems, there are also a number of benefits that should not be viewed as advantages. Following are some benefits of symmetric cryptography that distinguish it from other encryption techniques:
- Faster encryption and decryption times: Symmetric cryptography is often faster than asymmetric cryptography, which requires two different keys for encryption and decryption. This is the case because symmetric cryptography only needs one key to perform both operations.
- Large-scale data transmission performed more effectively thanks to symmetric encryption’s speed advantage over asymmetric cryptography.
- Symmetric cryptography is resistant to some sorts of attacks, such as known-plaintext attacks and ciphertext-only attacks, which provide stronger security. This is because the encryption technique uses a set key, making it more challenging for a hacker to decrypt the data without the key.
- Key management is often easier with symmetric cryptography because there is only one key needed, as opposed to asymmetric cryptography, which calls for two different keys.
- Public key exchange is not necessary: Symmetric cryptography just needs the key to be transferred between the sender and recipient, as opposed to asymmetric cryptography, which necessitates a public key exchange. This can make the encryption process easier, especially for smaller-scale data transmission.
Overall, symmetric cryptography has several advantages that are not considered drawbacks, such as faster encryption and decryption speeds, better performance for large-scale data transmission, stronger security against specific types of attacks, simpler key management, and no requirement for public key exchange. Symmetric cryptography is a useful encryption technique for many use cases thanks to these benefits, especially where speed and effectiveness are important considerations.
What are the key benefits of symmetric cryptography, and how do they compare to the potential drawbacks of the encryption method?
A single secret key is used by symmetric cryptography, a type of encryption, to both, encrypt and decode data. A common choice for data transmission and security, symmetric cryptography has several important advantages but also some possible downsides, such as the need for key distribution and the absence of built-in authentication.
The following are some of the main advantages of symmetric cryptography:
- Speed: Because of its lower computational and key operation requirements, symmetric cryptography is often significantly faster than asymmetric cryptography.
- Efficiency: Symmetric cryptography is frequently more effective than other encryption techniques because it only requires a single key, which is especially true when sending huge amounts of data.
- Symmetric cryptography can be extremely safe when used properly since the secret key is kept private and is inaccessible to unauthorized parties.
- Symmetric cryptography is a versatile solution for protecting data across many platforms because it is extensively supported by the majority of operating systems and software.
- Symmetric cryptography does, of course, have some potential disadvantages, such as the requirement for secure key distribution and the absence of built-in authentication. However, by carefully implementing best practices, these difficulties may frequently be overcome.
The main advantages of symmetric cryptography ultimately make it a potent instrument for securing data transmission and safeguarding sensitive information. Organizations can decide whether and how to use symmetric cryptography to fulfil their unique security needs by being knowledgeable about the benefits and potential drawbacks of this encryption technique.
How does symmetric cryptography enhance the security of data transmission, and what are some advantages that set it apart from asymmetric cryptography?
A common encryption technique called symmetric cryptography uses a single secret key for both encryption and decoding. This method differs from asymmetric cryptography in a number of ways, improving the security of data transmission in a variety of ways.
A few of symmetric cryptography’s main benefits are as follows:
- Speed: When compared to asymmetric cryptography, symmetric cryptography often provides faster encryption and decryption speeds. Because of this, it is a superior option for applications that need to transmit data in real-time or process massive amounts of data quickly.
- Resource Efficiency: Symmetric cryptography uses fewer resources than asymmetric cryptography, which uses many keys because it only needs a single key for encryption and decoding. Particularly for large-scale systems, this can lead to significant cost reductions.
- Key Management: Symmetric cryptography uses fewer keys than asymmetric encryption, making key management simpler. Key distribution to authorized parties and key revocation in the event of a key breach is now a simpler process.
- Attack Resistance: Symmetric cryptography is resistant to a variety of assaults, such as man-in-the-middle attacks and brute force attacks. This is because only those who have been given access to the shared secret key are aware of it, making it challenging for hackers to intercept or alter the data.
- Flexibility: Symmetric cryptography is extremely adaptable and can be used for a variety of purposes, including secure network security, file encryption, and secure messaging.
In conclusion, symmetric cryptography improves data transmission security by offering quick, effective, and adaptable encryption that is resistant to a variety of attacks. Symmetric cryptography is a well-liked and widely-used encryption approach in contemporary cybersecurity while having certain potential downsides.
In what ways can organizations leverage symmetric cryptography to improve their security posture, and what are some benefits that are not considered disadvantages?
Symmetric cryptography can be used by organizations in a number of ways to strengthen their security posture. Symmetric cryptography, commonly referred to as secret key cryptography, is a form of encryption that employs a single secret key for both data encryption and decryption.
Following are some advantages of symmetric cryptography that businesses can employ to strengthen their security posture:
- Speed: Symmetric cryptography is frequently more rapid than asymmetric cryptography, making it an excellent option for high-speed data encryption and decryption.
- Key management: Key management is made simpler for enterprises by symmetric cryptography, which only needs one secret key for encryption and decryption. In asymmetric cryptography, it is also simpler to distribute secret keys to permitted users than public keys.
- Compatibility: Symmetric cryptography can be integrated into an organization’s current security infrastructure because it is compatible with a wide range of devices and systems.
- Strength: Symmetric cryptography can offer effective security for data transport and storage when it is properly built and managed. It is especially helpful when encrypting huge amounts of data or when high-speed encryption and decryption are required.
- Efficiency: Symmetric cryptography is more effective and uses fewer computational resources than asymmetric cryptography, which can be very helpful for devices with limited resources.
- Protection: Symmetric cryptography can shield data in transit or at rest against eavesdropping, data manipulation, and other threats.
Organizations can strengthen their security posture by utilizing symmetric cryptography to protect their sensitive data and limit unauthorized access to it. Organizations can meet legal obligations, prevent data breaches, and preserve the confidentiality, integrity, and availability of their data by implementing strong symmetric cryptography. Moreover, symmetric cryptography can offer a practical solution to the growing need for efficient and secure data transmission brought on by the development of the Internet of Things (IoT) and other linked devices.
21 Best Ways to Use Symmetric Cryptography for Secure Data Transmission
Symmetric cryptography is an encryption technique that encrypts and decrypts messages using a single secret key. As a quick and reliable technique of data transmission security, it is widely used.
Following are 21 of the most effective applications of symmetric cryptography for safe data transfer:
- Encrypt sensitive emails and attachments to protect confidential information.
- Use symmetric encryption to secure online transactions, such as e-commerce purchases.
- Protect intellectual property by encrypting files and documents.
- Secure remote access to your organization’s network using symmetric encryption.
- Use symmetric cryptography to protect sensitive data stored on local devices, such as laptops and smartphones.
- Secure communication between two or more parties using symmetric encryption.
- Use symmetric encryption to secure data backups, both on-site and off-site.
- Encrypt passwords and other sensitive information stored in databases.
- Protect sensitive patient data in healthcare organizations with symmetric encryption.
- Use symmetric cryptography to secure online banking transactions.
- Encrypt sensitive financial data, such as credit card information and bank account numbers.
- Secure government and military communications with symmetric encryption.
- Encrypt files stored in cloud-based services to protect against unauthorized access.
- Secure electronic voting systems using symmetric encryption to prevent tampering.
- Use symmetric cryptography to secure VoIP communications.
- Encrypt files sent over peer-to-peer networks to protect against unauthorized access.
- Secure instant messaging and other forms of online communication with symmetric encryption.
- Use symmetric cryptography to secure data transfer between different operating systems.
- Encrypt data transmitted over wireless networks to protect against eavesdropping.
- Protect sensitive information stored on USB drives and other removable media with symmetric encryption.
- Use symmetric cryptography to secure any other form of data transmission that requires encryption.
You may be sure that your sensitive information is kept private and shielded from unauthorized access by utilizing symmetric cryptography to safeguard data transmission. Symmetric encryption is an effective technique for preserving the security of your data when sending emails, doing online transactions, or storing data locally or in the cloud.
Are there any unique advantages of symmetric cryptography that make it a more effective encryption method than asymmetric cryptography in certain scenarios, and if so, what are they?
Certainly, symmetric cryptography has special advantages over asymmetric cryptography in some situations, making symmetric cryptography a more effective encryption technique. These benefits include, among others:
- Faster Encryption and Decryption: When compared to asymmetric cryptography, symmetric cryptography methods employ the same secret key for encryption and decryption, which speeds up the process significantly.
- Lowered Overhead: Symmetric cryptography is a more efficient method for encrypting and decrypting huge volumes of data since it uses fewer computer resources in its implementation.
- Secure Key Exchange: Asymmetric cryptography calls for the exchange of both public and private keys, whereas symmetric cryptography just needs one key. Due to the fact that only the sender and receiver have access to the key, key exchange is now more secure.
- Reduced Complexity: Symmetric cryptography is easier to manage and implement in large-scale systems than asymmetric cryptography because it is less complex. It is also more practical in contexts with constrained resources because it uses less memory and computing power.
- Compatibility with Legacy Systems: Symmetric cryptography is frequently more compatible with legacy systems because asymmetric cryptography is not intended to be used with them.
- Enhanced Data Integrity: Symmetric encryption algorithms, such as AES (Advanced Encryption Standard), provide robust data integrity protection, ensuring that the data being transferred has not been tampered with or altered in any way.
Symmetric cryptography can, in some circumstances, provide stronger encryption than asymmetric cryptography. For instance, symmetric cryptography is frequently used in applications that demand high-speed data transmission, including video streaming, cloud computing, and other data-intensive ones. When data is exchanged between two parties who trust one another, such as across a closed network or a private communication channel, symmetric cryptography is also favored in these circumstances.
Generally, symmetric cryptography is a useful encryption technique in many situations where speed, efficiency, and compatibility with existing systems are key factors. Nevertheless, symmetric cryptography does have some limits.
How does symmetric cryptography facilitate secure communication, and what are some benefits that should be considered when evaluating the encryption method?
An encryption technique that enables secure communication between two parties is symmetric cryptography. This approach encrypts and decrypts communications using a secret key that is shared between the sender and the recipient. A few methods of symmetric cryptography that helps secure communication are the ones listed below:
- Confidentiality: Symmetric cryptography offers confidentiality as one of its main advantages. Every message encrypted with this secret key can only be unlocked by the receiver because only the sender and recipient are aware of it. This guarantees that the message is kept private and is not accessed by unauthorized persons.
- Integrity: Symmetric cryptography also makes sure that the message’s integrity, or whether it changes during transmission, is maintained. Any tampering with the message while it is being transmitted would result in the decryption process failing, which would be a sign that the message has been altered.
- Speed: Speed is a benefit of symmetric cryptography as well. Compared to asymmetric cryptography, which employs two keys, the procedure is quicker because only one key is needed for encryption and decryption.
- Efficiency: Symmetric cryptography is also resource-efficient. It uses fewer computer resources than asymmetric cryptography because the encryption and decryption operations are carried out using the same key.
- Compatibility: Symmetric cryptography is a common choice for securing communication in a variety of applications due to its compatibility with a wide range of communication protocols and hardware.
There are a number of things to take into account while assessing the encryption technique, including the robustness of the encryption algorithm, the length of the key, and the key management procedure. The simplicity of implementation, upkeep, and compatibility with current systems should also be taken into account. Depending on the application, it is also crucial to confirm that the encryption technique conforms with relevant industry standards and laws, such as the GDPR or HIPAA. Overall, symmetric cryptography has a number of advantages that make it a useful encryption technique for secure communication, particularly in situations where efficiency and speed are crucial considerations.
Conclusion: which is not a disadvantage of symmetric cryptography
Symmetric cryptography is a mechanism for encrypting and decrypting messages using a shared secret key. Despite the fact that symmetric cryptography has several problems, such as key management and lack of authentication, it remains a viable encryption technology for many enterprises due to its many advantages.
The speed of symmetric cryptography is an important advantage. As the same key is used for both encryption and decryption, the procedure is typically quicker than with asymmetric cryptography, which utilizes different keys for each process. This speed advantage can be crucial for enterprises that need to send big volumes of data rapidly and effectively.
The ease of symmetric cryptography is an additional benefit. Relative to asymmetric encryption, which can be more complex and challenging to implement, symmetric cryptography is comparatively simple. Its simplicity can make it simpler for enterprises to manage and employ, particularly if they lack the money or knowledge to adopt more complex encryption systems.
Symmetric cryptography provides a high level of security in addition to its speed and ease of use. While it is true that the security of the encryption method depends greatly on the secrecy of the key, symmetric cryptography can be extremely effective at preventing unauthorized access to sensitive data so long as the key is kept secret. The original communication can also be easily recovered by the intended recipient because the encryption procedure is reversible.
Moreover, it is important to note that symmetric cryptography can be exceedingly adaptable. It is commonly used for data transfer over networks or the Internet, but it can also be used to secure data on local systems and storage devices. Its adaptability makes it a versatile encryption technology that may be utilized in a variety of situations.
Symmetric cryptography has some limitations, such as key management and lack of authentication, but it also has a number of advantages that make it a highly successful encryption technique. It is an interesting solution for enterprises seeking to secure sensitive data due to its speed, simplicity, security, and versatility. When selecting whether symmetric cryptography is the best option for your firm, it is essential to analyze the risks and benefits, as with any encryption approach.