As organizations increasingly rely on complex networks to source, create, and deliver their products, the risk of cyber attacks in the global supply chain is increasing. Cybercriminals are constantly on the lookout for supply chain vulnerabilities, such as brittle linkages in third-party suppliers, old software and hardware, and human mistake.
Establishing thorough cybersecurity strategies that address the unique risks and difficulties of this complex ecosystem is necessary for businesses to reduce cyber attacks in the global supply chain. A proactive approach to risk management, teamwork with partners and suppliers, and routine testing and surveillance of security systems are required for this.
Finding and addressing vulnerabilities at every stage of the supply chain is one of the most important approaches to reduce cyber attacks in the global supply chain. This entails assessing and keeping tabs on the cybersecurity policies followed by partners and suppliers, putting best practices for data encryption and protection into place, and investing in systems that can quickly detect and stop cyberthreats. Companies can defend their global supply chains against cyberattacks, safeguard their brand, clients, and financial security by implementing best practices and taking a proactive approach to cybersecurity.
The Growing Threat of Cyber Attacks on the Global Supply Chain
• Suppliers, manufacturers, distributors, and logistics service providers are just a few of the many stakeholders in the global supply chain. As this ecosystem grows more digitalized, it also becomes more open to cyberattacks, which can have disastrous effects on both businesses and people.
• The fact that numerous parties with varying degrees of cybersecurity experience and resources are involved in the global supply chain is one of the main challenges to its security. This could lead to supply chain weaknesses that cybercriminals could take advantage of.
• To lower the danger of cyberattacks on the global supply chain, businesses need to take a proactive approach to cybersecurity, which involves ongoing testing and monitoring of their own systems as well as those of their partners and suppliers. This entails putting best practices for data protection, encryption, and access control into practice and investing in tools that can quickly identify and counteract cyber threats.
Collaboration amongst stakeholders is an additional crucial component of safeguarding the global supply chain. Sharing threat intelligence and best practices, working together on cybersecurity assessments and audits, and implementing standards and certifications that guarantee a minimum degree of cybersecurity throughout the entire supply chain are all included in this.
Common Cybersecurity Risks in the Supply Chain
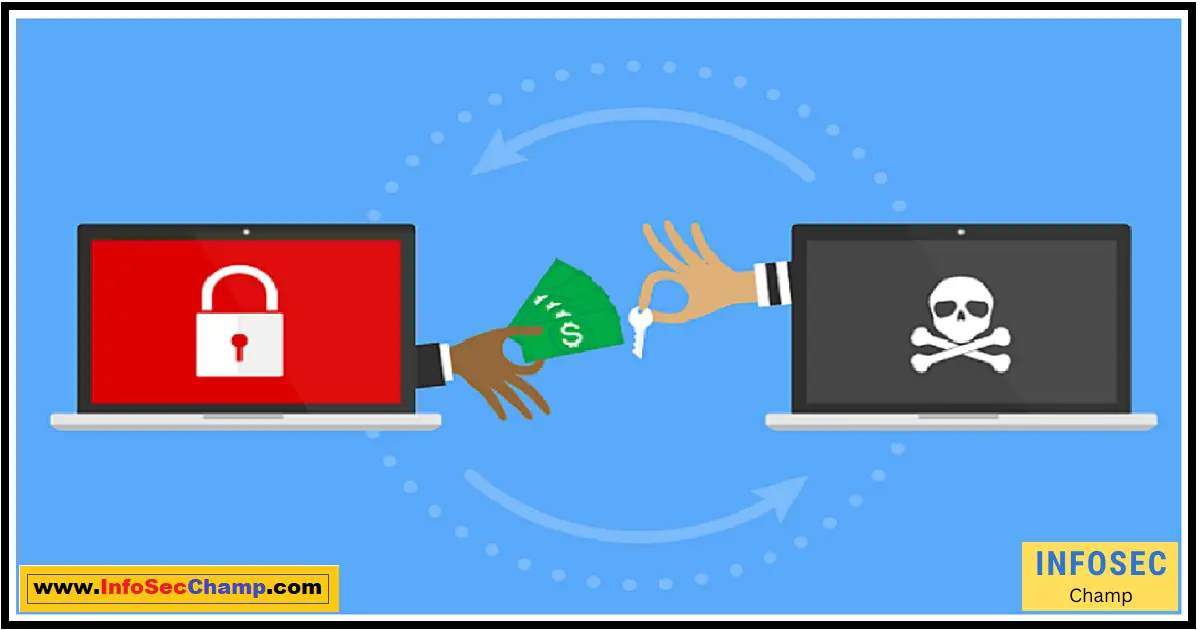
• Malware, phishing scams, ransomware, and insider threats are just a few of the cybersecurity hazards that the global supply chain is susceptible to. Suppliers, manufacturers, distributors, and logistics companies are just a few of the potential sources of these risks.
• Using out-of-date or insecure software and hardware is one of the most frequent cybersecurity concerns in the supply chain. Cybercriminals may be able to access sensitive data or interfere with business operations by taking advantage of these vulnerabilities.
• Employees and outside vendors that lack knowledge and training are another frequent concern. This may result in human error, such as opening a phishing email or unintentionally disclosing critical data.
• The usage of unreliable or untested third-party software and services might also result in supply chain vulnerabilities. This could open a backdoor for cybercriminals to assault the ecosystem of the supply chain.
• In order to reduce these risks, businesses need to put in place thorough cybersecurity policies and procedures that take into account the particular dangers and difficulties posed by the global supply chain. This entails carrying out routine evaluations and audits of partners and suppliers, putting best practices for data protection and access control into place, and delivering ongoing cybersecurity training to staff members and outside providers.
Best Practices for Supply Chain Risk Management
Effective supply chain risk management necessitates a proactive, all-encompassing strategy that handles the particular dangers and difficulties of the global supply chain. Every step of the supply chain, from sourcing and procurement to logistics and delivery, must be examined for vulnerabilities and addressed.
• Conducting routine risk analyses and audits of partners and suppliers is one of the best practices for supply chain risk management. Examining their financial viability, cybersecurity procedures, and adherence to pertinent laws and regulations are all part of this process.
Implementing best practices for data protection, encryption, and access control is another crucial component of supply chain risk management. This entails making sure that all sensitive data is encrypted both in transit and at rest, restricting who has access to sensitive data, and using multi-factor authentication to stop illegal access.
• By making investments in technologies that can identify and address risks in real-time, businesses can also lower the risk of cyber attacks in the supply chain. This covers systems for detecting intrusions and preventing them, as well as systems for managing security-related information and events and conducting ongoing security system testing.
• Another essential best practice for supply chain risk management is a collaboration with suppliers and partners. Sharing threat intelligence and best practices, working together on cybersecurity assessments and audits, and implementing standards and certifications that guarantee a minimum degree of cybersecurity throughout the entire supply chain are all included in this.
• Lastly, businesses need to have a strong incident response strategy in place so that they can react swiftly and successfully to supply chain cyberattacks. A clear chain of command, protocols for communication and coordination, and a strategy for business continuity and recovery are all part of this.
The Role of Collaboration in Supply Chain Cybersecurity
Effective supply chain cybersecurity depends on cooperation between parties. Sharing threat intelligence and best practices, working together on cybersecurity assessments and audits, and implementing standards and certifications that guarantee a minimum degree of cybersecurity throughout the entire supply chain are all included in this.
• By collaborating, businesses, their suppliers, and their partners may find and fix weaknesses in the ecosystem of the supply chain, exchange knowledge about new dangers and methods of attack, and put best practices for data security and access control into effect.
The requirement for transparency and trust among stakeholders is one of the main obstacles to collaboration in supply chain cybersecurity. Clear policies and processes for information sharing as well as carrying out joint assessments and audits are necessary for this. It also calls for a culture of openness and cooperation.
• Striking a balance between corporate goals and requirements while maintaining security is another difficulty. All supply chain participants, including those in procurement, logistics, and operations, must work together to achieve this.
• To address these issues, businesses need to take a proactive, all-encompassing strategy to cybersecurity that involves working with partners and suppliers, continuously testing and monitoring security systems, and fostering an environment that values innovation and continuous development.
Steps to Take When a Cyber Attack Occurs in the Supply Chain
• Security breaches may still happen despite the greatest attempts to stop cyberattacks in the supply chain. Companies must act quickly after a cyber assault happens in order to reduce the impact and stop additional damage.
• The first stage in stopping the attack’s propagation is to confine and isolate the systems and data that have been compromised. This entails cutting off the network connection to the impacted systems, blocking user accounts and passwords, and keeping track of any relevant data for forensic investigation.
• Businesses must also inform all parties involved in the supply chain, such as partners, customers, and suppliers, of the breach and promptly and clearly communicate the actions being taken to address the issue.
• The following action is to carry out a thorough assessment of the attack to identify its primary causes, the extent of the damage, and any potential effects on operations and clients.
• Businesses should also take action to address the incident, such as putting security patches and upgrades into place to close holes in their defenses, restoring backups of the affected data, and enhancing security protocols to thwart future assaults.
• In order to identify lessons learned and areas for improvement, businesses should undertake a post-mortem review of the attack. It also entails undertaking further security assessments and audits, revising incident response protocols, and implementing cybersecurity best practices throughout the whole supply chain.
The Future of Supply Chain Cybersecurity: Trends and Predictions
• The risk of cyber attacks is only anticipated to rise as the global supply chain continues to develop and become increasingly digitalized. Companies need to be aware of upcoming supply chain cybersecurity trends and projections if they want to stay ahead of the curve.
• One of the major trends is the growing reliance on machine learning and artificial intelligence to quickly identify and address cyber threats. These tools can be used to spot data anomalies and trends that can be signs of an impending assault. They can also automate incident response processes to lessen the effects of an attack.
• The importance of supply chain transparency and visibility is another trend. To maintain a secure and transparent record of all transactions and interactions in the supply chain, businesses are increasingly utilizing distributed ledger technologies like blockchain. By spotting holes and weaknesses in the ecosystem, helps enhance supply chain risk management and stop cyberattacks.
• The third trend is a greater emphasis on business continuity and supply chain resilience. Businesses must have measures in place to swiftly recover from an attack and reduce its impact on operations and customers as cyberattacks become more sophisticated and disruptive.
• Lastly, supply chain cybersecurity is placing more and more importance on collaboration and partnerships. Companies are recognizing that they cannot protect the supply chain ecosystem on their own and are developing partnerships with suppliers, partners, and other stakeholders in order to exchange threat intelligence, carry out joint assessments and audits, and follow best practices for data protection and access control.
Conclusion for cyber attacks in global Supply chain
Supply chain security against cyberattacks is more important than ever in the globalized and digitalized world of today. Companies must implement a proactive, all-encompassing strategy for supply chain cybersecurity given the frequency and sophistication of cyberattacks.
This entails identifying and fixing weaknesses at every stage of the supply chain, working with partners and suppliers, putting best practices for data protection and access control into place, and spending money on technologies that can recognize and respond to threats instantly. Companies may lessen the damaging effects of cyberattacks by adopting these precautions to protect their reputation, consumers, and bottom line.

FAQs:
What is supply chain cybersecurity? | cyber attacks in global supply chain
A: Supply chain cybersecurity is the process of detecting and reducing cybersecurity risks in the international ecosystem of the supply chain, which comprises numerous stakeholders like suppliers, manufacturers, distributors, and logistics providers.
What are the common cyber risks in the global supply chain?
The usage of old or insecure software and hardware, a lack of knowledge and training among employees and outside suppliers, the utilization of unprotected or untested third-party software and services, and human mistake are among the frequent cyber dangers in the global supply chain.
How can companies reduce cyber attacks in the global supply chain?
A: Businesses can reduce cyber attacks in the global supply chain by implementing best practices for data protection, encryption, and access control, investing in technologies that can identify and counteract cyber threats in real-time, and working with suppliers and partners.
Golden Quote:
“Collaboration and partnership are the keys to effective supply chain cybersecurity.”